|
But if you have good data backups, there is no need to search for keys. So, if you still need to create good backups, then do it now. Maybe section 7 provides some usable tips, or follow any other good method, you are comfortable with. |
|
Rule Number 1: => Always have good and recent backups of all your valuable data, and store them savely at another location (e.g. not on the same PC, and not online). Most ransomware is able to enummerate (discover) all local drives, and network drives mounted on the system. That's why you must disconnect the backupdrive(s) after a backup is done. Otherwise your backupdrive(s) can be encrypted too. => Have multiple backups (recent, and slightly older ones), to make sure you are good. =>Only rely on multiple media. For example, having only "1" backup device, is not good. Super trivial remarks ofcourse..., sorry about that. (this applies ofcourse only for a personal user, and ofcourse not for companies, datacenters etc... That's ofcourse totally evident. Just saying...) |
|
Rule Number 2: Be very careful with email attachments and links in emails. Those are very common causes (among others), for ransomware infections. In effect: only open an attachment if you are confident of the source, or the document is exactly what you already expected to recieve. It's really true: not withstanding all the nifty tricks around, the simple attachments and links in emails (and sites) are the main cause for infections. You can avoid that. Other "relatively mundane" causes are that (general) trojans may drop the ransomware, or you get it via download of untrusted tools, or installers, containing the malware etc... So, you better not stuff your business PC with all sorts of shady "tools", which you can find all over the place. |
|
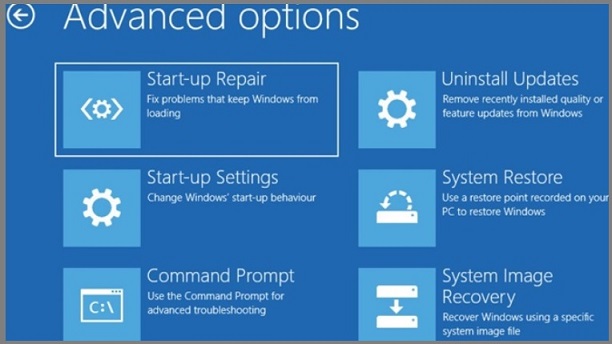
Some further pointers to investigate: (1). Do not use your PC with an Admin account. (2). Maybe you like to investigate using Virtual Machines: if one goes "down" using the internet, it's easy to restore, and the thing is quite isolated from the rest (other VM's). However, using VM's is not the holy grail against ransomware. Also, it can be a challenge to learn about VM's if you are quite blank to the technology. (3). Use easy to mount and unmount backup media. Always unmount after creating a backup. (4). Maybe you can use an older PC as a "backup server", which is *only* online on your network, when needed. (5). Make sure the firewall is on, and optionally tuned for your system. (6). If needed, make a study of controlled folder (directory) access, like NTFS permissions granted to some users (groups) only, and not to general groups like "Everyone" or "Authenticated Users". (7). If you want, you may investigate how you can lower the number of running services, shutdown ports etc.. all for the sake of lowering your "surface area of attack". There are lots of Cyber documents which give good pointers for this. (8). Try to create a "repair disk" like bootable DVD, or bootable USB, with WinRE/WinPE (a mini windows). (9). Extremely trivial: apply OS patches and application patches. (10). Really Hyper trivial: use good, and licensed, well-known Anti Virus software. Sorry for the trivial remarks... |
|
-In general: Reinstall the System (or restore image) + restore datafiles, EXCEPT if you know for sure, that in your specific case (with your specific ransomware), it's good enough to follow method (2). -Important: The above, represents my own view only. Most articles do not refer to a reinstall of the OS. They describe a procedure similar to method (2). So, if you prefer (2) above (3), that could be right. I only wanted to exclude any risks. |
|
Some recommendations: =>Especially to counteract ransomware: Ransomware is often able to ennumerate (discover) all storage you have available on your PC (like C:, D:, F:, U: etc..., and possibly even UNC paths). So, after a backup is Done, then (nicely) disconnect the backup device (like usb disk, or backup Server etc..). =>Also important: Having very recent backups is great. But keeping slightly older backups, (a few days old, a week old or so, all up to you) is highly recommended. =>Only rely on multiple media. For example, having only "1" backup device, is not good. =>It helps if you have "organized" (most) of your datafiles, in some main folder, and subfolders, where each subfolder contains some particular type of data, like: E:\DATA, and within E:\DATA, subfolders like E:\DATA\EXCEL, E:\DATA\PHOTOS, E:\DATA\ACCOUNTING, E:\DATA\MSWORD etc.. etc.. |
|
First, goto U: and if neccessary, create directory DATA. |
U: cd\ md DATA |
|
Goto the datadrive E: again, change to E:\DATA, and use "xcopy" |
E: E:\> cd \DATA E:\DATA> xcopy *.* U:\DATA /S |
|
=>File extensions after encryption: |
|
=>File extensions after encryption: Often: .WNRY, .WNCRY, .WNCRYT, .WRCY |
|
=>File extensions after encryption: Often, or exclusively sofar: .clop |